Cybersecurity & Cyber Crime Investigation (40 Courses)
Master the skills to safeguard digital systems, detect cyber threats, and investigate online crimes. This collection of 40 in-depth courses covers ethical hacking, digital forensics, cyber laws, penetration testing, and more—equipping you to protect organizations and fight against cybercrime effectively.

- 20 Modules
- 420 Students
Ethical Hacking
Learn to legally hack systems to discover security flaws before real attackers do. This
course teaches network scanning, system exploitation, and securing digital
environments — making you a certified white-hat hacker.

- 10 Lessons
- 6 Studenst
Penetration Testing
Dive deep into offensive security by simulating advanced attacks on web apps,
networks, and APIs. This training sharpens your ability to find and patch real-world
vulnerabilities.

- 22 Modules
- 1680 Students
Cyber Crime Investigation
Master digital crime-solving skills including evidence gathering, IP tracing, cyber fraud
detection, and investigating cases like identity theft, phishing, and online stalking.

- 10 Lessons
- 6 Studenst
Digital Forensics
Learn to extract, preserve, and analyze data from digital devices in a legally admissible
format. A must-have skillset for law enforcement and forensic teams.

- 10 Lessons
- 6 Studenst
Malware Analysis
Understand how malicious software behaves, spreads, and infects systems. This
course trains you to reverse malware, analyze payloads, and design defenses
- 10 Lessons
- 6 Studenst
Reverse Engineering
Explore the core of compiled applications, uncover malware logic, decrypt executables,
and learn anti-analysis techniques.

- 10 Lessons
- 6 Studenst
OSINT (Open Source Intelligence)
Use advanced tools and techniques to gather actionable intelligence from public
sources. Ideal for cybersecurity analysts, journalists, and investigators.

- 10 Lessons
- 6 Studenst
Network Security
Secure enterprise networks using firewalls, intrusion detection systems (IDS), VPNs,
and segmentation techniques. Learn how to design and defend secure network
architectures.
- 10 Lessons
- 6 Studenst
Web Application Security
Learn how hackers exploit web applications and how to defend against them using the
OWASP Top 10, secure coding practices, and vulnerability scanning tools.

- 10 Lessons
- 6 Studenst
Incident Response & Handling
Train to react quickly and effectively to cyber incidents like data breaches, DDoS
attacks, and system intrusions. Build resilience and response strategies

- 10 Lessons
- 6 Studenst
Red Team Operations
Conduct simulated attacks mimicking real adversaries to test an organization’s defense
posture — using tools like Cobalt Strike and Metasploit.
- 10 Lessons
- 6 Studenst
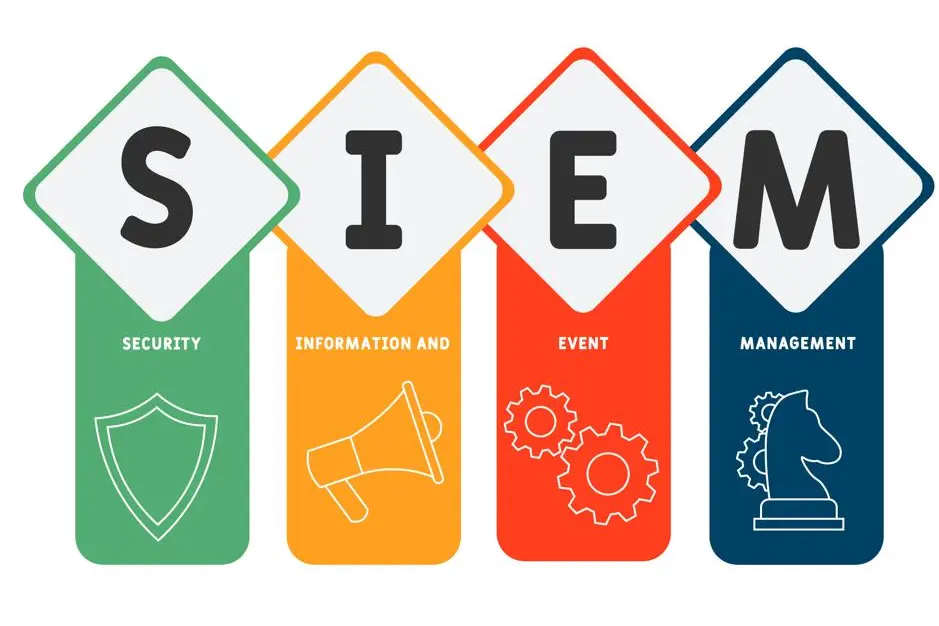
Blue Team Operations
Learn the defense side of cybersecurity — threat monitoring, log analysis, anomaly
detection, and post-attack recovery using SIEM tools.

- 10 Lessons
- 6 Studenst
Cyber Threat Intelligence (CTI)
Collect and analyze threat data to predict and prevent attacks. Learn threat modeling,
IOC analysis, and use of platforms like MISP.

- 10 Lessons
- 6 Studenst
Ransomware Defense & Recovery
Conduct simulated attacks mimicking real adversaries to test an organization’s defense…

- 10 Lessons
- 6 Studenst
Cryptography & Encryption
Learn modern cryptographic techniques including AES, RSA, hashing, and digital
signatures to secure data in transit

- 10 Lessons
- 6 Studenst
Cloud Security
Secure cloud infrastructure across AWS, Azure, and GCP. Learn IAM, encryption,
shared responsibility models, and cloud-native threat detection.

- 10 Lessons
- 6 Studenst
IoT Security
Learn to identify risks in Internet of Things ecosystems and secure devices from botnet
attacks, data leakage, and unauthorized..

- 10 Lessons
- 6 Studenst
Mobile App Security
Learn to analyze and secure Android and iOS applications from threats like reverse
engineering, code injection, and insecure data storage.

- 10 Lessons
- 6 Studenst
SCADA/ICS Security
Protect critical industrial systems from sabotage and intrusion. This course focuses on OT protocols, threat modeling, and SCADA-specific vulnerabilities

- 10 Lessons
- 6 Studenst
Dark Web Investigation
Safely explore the dark web using Tor and other tools to uncover illegal marketplaces
and threat actors.
- 10 Lessons
- 6 Studenst
Email Security & Phishing Defense
Detect and prevent email-based threats using SPF/DKIM/DMARC, sandboxing, and
user awareness strategies.
- 10 Lessons
- 6 Studenst
Social Engineering & Human Hacking
Study how attackers manipulate people to gain access. Learn to defend against
phishing, baiting, vishing, and impersonation.

- 10 Lessons
- 6 Studenst
Cyber Law & Policy
Understand the legal aspects of cybersecurity including IT Act, GDPR, cyber evidence
handling, and digital rights

- 10 Lessons
- 6 Studenst
Insider Threat Detection
Learn to identify, monitor, and manage risks posed by malicious or negligent insiders..
- 10 Lessons
- 6 Studenst
Security Information & Event Management
Monitor and analyze security data using tools like Splunk, IBM QRadar, or ELK stack.

- 10 Lessons
- 6 Studenst
Bug Bounty & Responsible Disclosure
Learn to hunt bugs on real platforms, report responsibly, and earn rewards through
HackerOne and Bugcrowd.

- 10 Lessons
- 6 Studenst
Wi-Fi Hacking & Wireless Security
Learn to audit wireless networks, crack passwords, and implement WPA3 and
radius-based enterprise security.

- 10 Lessons
- 6 Studenst
Digital Identity & Access Management (IAM)
Secure access to systems using role-based access control, multi-factor authentication,
and SSO

- 10 Lessons
- 6 Studenst
Cybersecurity for Law Enforcement & Police
Tailored training for police officers and cyber cells to solve digital crime with efficiency and accuracy.

- 10 Lessons
- 6 Studenst
Cyber Hygiene & Awareness (For All)
Basic course for students and professionals to follow safe digital practices and prevent
being hacked.

- 10 Lessons
- 6 Studenst
Computer & Mobile Forensics
Extract deleted files, messages, call logs, and app data from computers and mobile
phones for investigations.
- 10 Lessons
- 6 Studenst
Security Operations Center (SOC) Analyst
Train for real-time threat monitoring, triage, and escalation roles using real-world tools.

- 10 Lessons
- 6 Studenst
Endpoint Detection & Response (EDR)
Learn to detect and respond to threats on endpoints using advanced security platforms.

- 10 Lessons
- 6 Studenst
Vulnerability Assessment & Remediation
Scan systems for weaknesses and fix them using risk-based prioritization and patching
strategies.

- 10 Lessons
- 6 Studenst
Secure Coding Practices
Prevent security bugs at the coding level using input validation, session management,
and secure storage.

- 10 Lessons
- 6 Studenst
Cryptocurrency Investigation
Learn blockchain tracing, transaction analysis, and wallet monitoring to fight
crypto-based crime.

- 10 Lessons
- 6 Studenst
Cybersecurity in Healthcare Sector
Secure patient data, medical devices, and hospital networks from cyber threats

- 10 Lessons
- 6 Studenst
AI in Cybersecurity
Use artificial intelligence to detect, analyze, and prevent cyber threats in real time

- 10 Lessons
- 6 Studenst
Zero Trust Security Architecture
Eliminate implicit trust and implement strict access controls in modern IT environments.

- 10 Lessons
- 6 Studenst
Cybersecurity Internship Program
Hands-on experience with real incidents, tools, and reporting — perfect for building a
career in security.

- 10 Lessons
- 6 Studenst
AI in Cybersecurity
Use artificial intelligence to detect, analyze, and prevent cyber threats in real time
- 10 Lessons
- 6 Studenst
Zero Trust Security Architecture
Eliminate implicit trust and implement strict access controls in modern IT environments.

